
Why Cybersecurity Matters More Than Ever for Small Businesses
Introduction In the present digital we see why cybersecurity matters more than ever for small businesses, to run their day…
Well-Researched Information You Can Trust

Introduction In the present digital we see why cybersecurity matters more than ever for small businesses, to run their day…

Today’s business context is completely web-based, and the survival of any organization depends on the strength, velocity and reliability of…

As the world becomes increasingly connected, safeguarding against cyber threats is more crucial than ever, especially in our personal and…

Introduction In our present digital age computers are at all times transmitting and storing large scales of info. From the…

Introduction Nowadays, we live in the digital era and the internet has turned into a huge network where millions of…

In the contemporary digitized world, computers are at all times vulnerable to diverse cyber-attacks such as malware attacks, unauthorized access,…

Managed services replace variable, reactive spending with steady, planned investments that align to service levels. Flat fees cover monitoring, patching,…
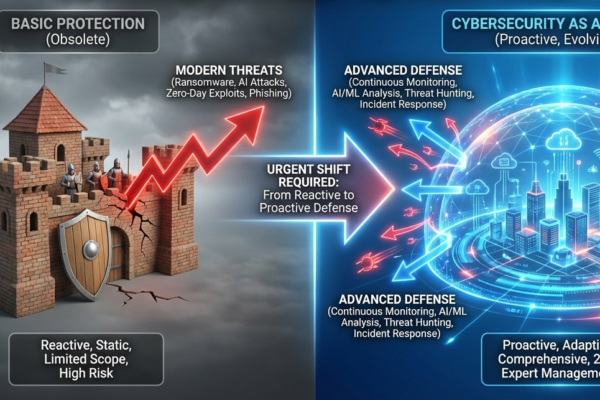
There has never been a more digitally connected business environment as seen today. The cloud environments, remote working forces, mobile…

Cybersecurity is emerging as one of the most important issues of people, companies, and governments in an interconnected world. Digital…

The Internet is now a very useful device of communication, business, education and activities in the highly connected world. Since…

As the world becomes ever more interconnected, the importance of robust cybersecurity measures continues to escalate. With the dawn of…

The issue of cybersecurity is one of the most important areas of contemporary digital space. With the increasing technological advancement…

Introduction: The Emerging Demand of Digital Security Today, we live in a highly connected society where individuals keep all the…

In the hyper-connected world today, our devices, apps and operating systems are critical to our work, communication, shopping, learning and…

Privacy is one of the most precious and the most threatened commodities in the hyper connected world today. All the…

With the modern digital era, social media platforms have entered society. They bind us with friends, family and societies throughout…
In the world of today, which is more connected than ever, the protection of your online accounts is more important…

The modern interconnected world is no longer luxurious; it has become mandatory to have access to the internet. In the…

In the age of increasingly advanced cyber dangers and credential theft being among the leading reasons of breaches, organizations are…

Introduction: The Moving Ground of Authentication Security in the workplace has always been a balancing game between ensuring the confidentiality…

Introduction In digital-first workplaces today, workers use dozens of business apps daily. Project management software, communication software, cloud storage, customer…

Introduction The average employee in the modern workplace is supposed to handle dozens of online accounts in one day. These…

However, cybersecurity has become a battlefield with more advanced forms of threats, more often and more unexpectedly. The organizations can…

When it comes to privacy, security, or unblocking geo-restricted content, proxy servers play a major role in your online experience….