As the world becomes increasingly connected, safeguarding against cyber threats is more crucial than ever, especially in our personal and professional lives. Every data transfer worldwide is a potential opportunity for bad actors to exploit vulnerabilities to benefit themselves financially, politically or simply to cause disruption. Network security concepts is more than a policy or a technical solution for an IT department; it’s a cornerstone for the stability of today’s society. In a world filled with growing complexity and an ever-connecting array of devices, it is becoming a vital safety skill to know how to protect these systems from cyber attacks. It’s an in-depth look at the mechanisms that ensure that our data remains safe, the key components that make up a strong security stance against a constantly changing landscape of digital threats.

Understanding Core Network Security Concepts

Recognize core concepts of network security. Be familiar with concepts of network security. A solid base in any defensive strategy relies on learning the basics of Network Security that will help create a secure environment. Network Security, in essence, is concerned with keeping the information confidential, intact and accessible (known as the CIA Triad). The three pillars of information security—confidentiality, integrity, and availability—are all essential to ensuring that sensitive information is accessed by only those who are authorized, that it remains consistent and free from changes during transit, and that systems and data are available to those who need them. Organizations can adopt layers of defense, including physical security, administrative policies, and technical controls, to create a “defense-in-depth” approach that makes it much more difficult for an attacker to be successful, even if one layer is overcome.
Common Cyber Threats
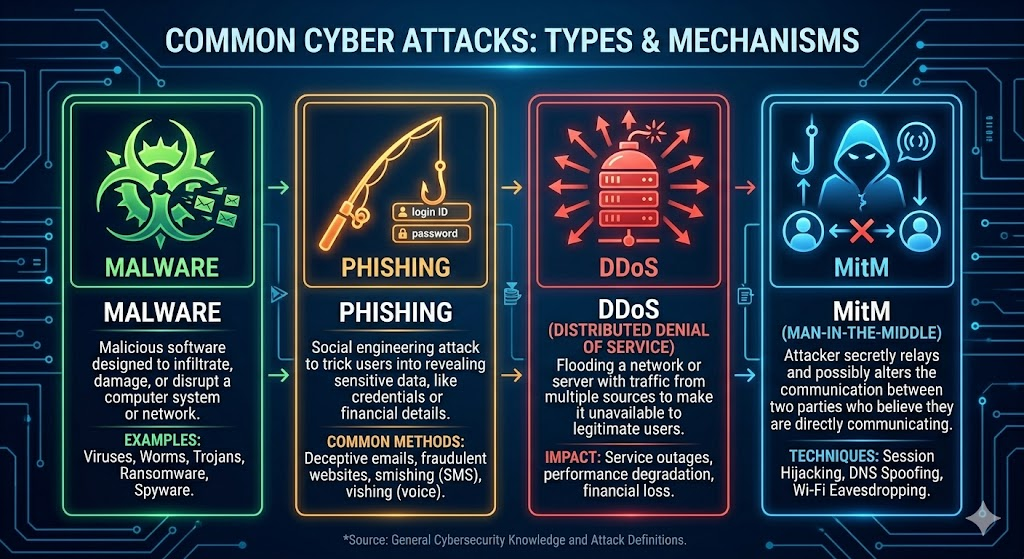
The web is full of attacks from automated “bots” looking for open ports to highly advanced “Advanced Persistent Threats” (APTs) from well-funded forces. Common risks include attacks with malware, such as viruses and ransomware, which can hold entire infrastructures hostage, as well as phishing, which targets individuals and prompts them to give up their credentials. In addition, Distributed Denial of Service (DDoS) attacks are designed to flood servers with traffic, making their services impractical to use and Man-in-the-Middle (MitM) attacks are designed to intercept private communications. The key to mitigating these threats is to identify them and then adapt security measures to their network environment in order to prevent the most likely vulnerabilities being exploited.
Firewalls: The First Line of Defense

A firewall is like a watchdog standing on the boundaries of a network, watching and regulating traffic that comes in and out, according to the rules and security policy established for it. Imagine a security guard at the entrance of a private building, who checks identification to make sure only people who have a business there are allowed in. Firewalls may be hardware, software or cloud-based. Their main purpose is to create a defense that separates a trusted internal network from an untrusted external network, like the Internet. A firewall can analyze “packets” of data, blocking access for people who are not supposed to be on it, and allowing data to go out of the system. A firewall can prevent hackers from getting a foot on the boat before they even start their attack.
A modern firewall has grown beyond the basic packet filtering. Today, we’re using Next-Generation Firewalls (NGFWs), a type of firewall that has deep packet inspection (DPI) capabilities, which means it will inspect the data itself as well as the header (the source and destination addresses). The firewall can then detect and prevent advanced threats or secret attacks that conventional firewalls may not. Also, stateful inspection firewalls monitor the status of connections that are already established with devices inside the network, so that the inbound traffic is a valid response to an inbound request. Firewalls continue to be an essential part of network security, offering a powerful barrier against the first phases of a cyber-attack with capabilities such as application awareness and integrated intrusion prevention.
Encryption: The Shield of Privacy

Encryption is the conversion of clear text that is easily read into a pattern of characters or numbers called ciphertext that cannot be read without the key that originally encrypted it. This makes it so that if an attack is able to grab a data transmission, the data is of no use to the attacker without the decryption key. From credit card transactions to medical records, private emails to corporate trade secrets, encryption plays a crucial role in safeguarding all of these. It works on two main levels: data at rest (on hard drives, or in a database) and data in transit (traveling across the internet). With robust encryption practices, organizations can maintain a high level of privacy and keep their most sensitive assets confidential from any point to point.
There are two types of encryption: Symmetric encryption and Asymmetric encryption. Symmetric encryption is used in situations where large amounts of data are to be encrypted and can be decrypted quickly and easily, and it requires one key for both encryption and decryption. The difficulty is sharing that key securely between the parties, however. Asymmetric encryption (public-key encryption or private-key encryption) overcomes this problem by providing two keys: a public key that can be used to encrypt data and a private key that can be used to decrypt it, but is only known to the recipient. These two-key mechanisms are used to create two protocols – Secure Socket Layer (SSL) and Transport Layer Security (TLS) – that are represented by the padlock. With so many data breaches happening in the world, encryption is the last and most robust line of defense for data privacy.
Authentication and Access Control
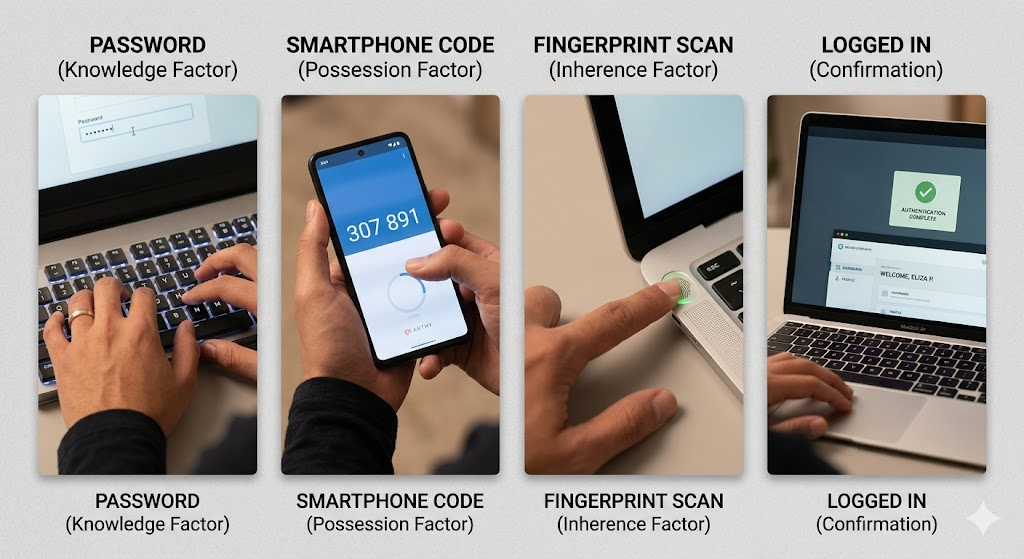
The purpose of this course is to examine the authentication and access control mechanisms used to verify identity. Authentication is a strict procedure of verifying whether a user or system is who they say they are prior to granting access to a network resource. A username and password would have been sufficient for the past, but with this heightened risk environment, “something you know” is not enough. Multi-Factor Authentication (MFA) is the industry standard today, which mandates that users enter two or more factors of authentication. That usually requires a password, a physical item and a code sent to a smartphone, as well as biometric data such as fingerprints or facial recognition. If an attacker gained access to the system, it would require him or her to breach several independent factors to access the system, and that is where MFA comes into play.
After authentication a user gets what he/she can see and do in a network, which is decided by Access Control. The principle of least privilege (PoLP) is generally followed when assigning these, and states that users should only be given the minimum access they need to complete their job functions. For example, administrative privileges should not be given to a marketing intern to access the company’s financial servers. With the integration of Role Based Access Control (RBAC), organizations can classify users into groups and grant access privileges to groups instead of users, making it easier to manage and decrease the chance of what is called “privilege creep.” The impact of a compromised account is contained to a specific area of the network with strict access control.
Constant Vigilance: Intrusion Detection and Prevention Systems

Firewalls protect the outside of the network, and Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are the internal security cameras and automated response teams of a network. IDS is a system that constantly watches network traffic for unusual activity or patterns of attacks and notifies an administrator if a possible threat is found. It is a passive system that can give visibility of the “east-west” traffic that is moving within the network, and that is important to detect attackers who are able to penetrate the perimeter defenses. Logs and traffic flows can be used by an IDS to determine the extent of an intrusion and to manually respond to the intrusion and stop the damage.
An IPS goes further than simply detecting threats and takes proactive steps to prevent them, in real-time. If an IPS detects a malicious packet or a security policy violation, it may block the packet, terminate the connection or block traffic from the offending IP address. They typically rely on signature-based detection, which compares traffic with a database of known attacks, and anomaly-based detection, which looks for activity that deviates from “normal” network traffic. It’s a two-part approach that’s important in protecting against “zero day” attacks, where a new vulnerability is discovered and a patch or signature is not available. IDS and IPS are complementary technologies that work together to create a continuous, automated monitoring and defense system crucial for a secure network environment.
Practical Measures to Protect Infrastructure
While technical tools are important components of network security, it’s equally crucial to have a comprehensive strategy for establishing network security, which involves proper maintenance, policy implementation, and user awareness. Continuous patching and software updates is one of the best strategies. Hackers attack known vulnerabilities in operating system and application software; staying up to date means you’re closing the doors they’re trying to walk through. Furthermore, network segmentation (subnets) can block the lateral movement of attackers. A failure in one segment will not affect the other segments, thus reducing the “blast radius” of the failure and facilitating the identification and mitigation of the failure by security teams.
Additionally, it’s crucial to build a security-conscious culture amongst staff. People are still the number one cause of security breaches today, whether by using weak passwords that can be guessed, or falling for a phishing scam. Frequent training programs can help employees identify warning signs of cyber threats and what they can do to safeguard their company’s data. In addition to the human element, they should also conduct periodic security audits and penetration testing at the organization. These “fire drills” are designed to simulate an attack to discover any weaknesses in the infrastructure before an attacker can. With the latest technology, a proactive management approach and an educated workforce, any organization can fortify its security against all the threats of the digital world.



