Many small businesses think they are too small to be targeted by cyberattacks. However, attackers know that smaller companies often have fewer security measures, which makes them easier targets. Even a single breach can result in lost data, financial damage, and a damaged reputation. Many small business owners rely on basic security tools like antivirus software or firewalls, but these alone are not enough to protect against modern cyber threats.
Penetration testing is a practical way to assess your business’s security. It simulates real-world attacks to identify weak points in systems, networks, and applications before malicious hackers can exploit them. By uncovering vulnerabilities, business owners can take action to strengthen defenses, protect sensitive data, and maintain smooth operations. Regular testing also helps prepare your team for potential incidents and ensures ongoing improvements to security measures. Connect with trusted Penetration Testing Services experts in Los Angeles to quickly secure your small business, identify vulnerabilities, and protect your systems from cyber threats.
In this blog, we will explore penetration testing, its importance, and the steps for small businesses.
What Is Penetration Testing?
Penetration testing involves simulating a cyberattack on a business’s systems, networks, or applications to identify security weaknesses. It helps uncover vulnerabilities before real hackers can exploit them, allowing companies to strengthen defenses, protect sensitive data, and improve overall security. It is a proactive approach to safeguard digital assets and maintain business continuity.
Importance of Penetration Testing for SMBs
Penetration testing helps keep your small business safe from cyber threats. It is more than just a technical task. It enables you to understand where your systems, networks, and applications might be vulnerable, so you can take action before attackers do. Some key benefits include:
- Protect Sensitive Data: Identify weaknesses that could expose customer information, financial records, or business secrets, keeping them safe from hackers.
- Prevent Financial Loss: Cyberattacks can be costly. Penetration testing helps you fix vulnerabilities early, reducing the risk of expensive breaches or downtime.
- Strengthen Customer Trust: Showing that you take security seriously reassures clients and partners, building credibility and long-term loyalty.
- Test Security Controls Effectiveness: Penetration tests reveal whether your current security measures are working or need improvement, helping you make informed decisions.
By understanding these benefits, small businesses can proactively secure their digital assets and operate confidently in today’s cyber threat landscape.
8 Steps to Penetration Testing for Small Businesses
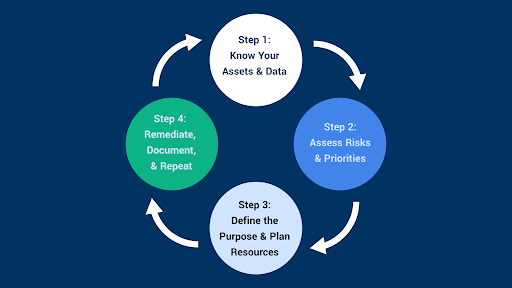
Penetration testing helps you understand and improve your business’s security. By following a precise sequence of steps, small businesses can identify vulnerabilities, prioritize actions, and maintain a resilient security posture. The following steps provide a comprehensive guide to conducting penetration testing effectively, ensuring your systems, networks, and data remain secure.
- Planning and Scoping
Planning and scoping set the basis for a successful penetration test. This step involves identifying business-critical assets, defining objectives, and establishing the scope of testing. Clear boundaries ensure that testing focuses on the most critical systems and avoids unnecessary risks. Rules of engagement are defined to ensure tests remain safe and controlled.
Effective planning helps align penetration testing with business priorities, ensuring maximum value and actionable insights without disrupting operations. Proper planning transforms testing from a technical activity into a strategic business tool.
- Threat Modeling
Threat modeling helps identify potential risks to the business by considering likely attack systems and their potential impact. It assesses the vulnerabilities of systems, applications, and networks to determine the most critical areas to focus on. This step allows businesses to prioritize resources, ensuring the most significant threats are addressed first.
By understanding potential attackers and their methods, threat modeling guides the testing process and creates a roadmap for uncovering hidden vulnerabilities efficiently. It strengthens the overall security strategy and business resilience.
- Vulnerability Assessment
Vulnerability assessment scans systems and applications to detect weaknesses that could be exploited. This step provides a clear picture of security gaps and assigns risk levels to each finding. Prioritization allows businesses to focus on high-risk vulnerabilities that could cause significant damage.
Regular vulnerability assessments help maintain a proactive approach to cybersecurity by continuously identifying and addressing potential threats. The assessment process builds a detailed inventory of weaknesses and informs the next steps of penetration testing, ensuring targeted and effective security improvements.
- Exploitation
Exploitation involves safely testing identified vulnerabilities to evaluate the potential impact of a real attack. This step shows how weaknesses could be exploited and the extent of possible access or damage. It helps prioritize remediation efforts based on real-world risk.
Safe exploitation ensures no disruption to business operations while providing valuable insights into security gaps. By simulating attacks, businesses gain a realistic understanding of their exposure and can take informed actions to protect sensitive data and critical systems.
- Post-Exploitation Analysis
Post-exploitation analysis evaluates the results of the exploitation phase to understand the effects of potential breaches. This step examines the level of access attackers could achieve, the data at risk, and how vulnerabilities could lead to further compromise.
Post-exploitation analysis provides a clear view of the business’s security posture and highlights areas that require immediate attention. It is essential for creating an actionable roadmap for improving defenses and strengthening the overall security strategy.
- Remediation Planning
Remediation planning translates penetration test findings into concrete actions. Vulnerabilities are prioritized, and strategies are developed to address weaknesses efficiently. This step involves collaboration between IT teams and business decision-makers to implement solutions such as patching systems, updating configurations, and enhancing security policies.
Effective remediation ensures vulnerabilities are resolved promptly, reducing exposure to cyber threats. Planning remediation carefully transforms insights from testing into measurable improvements in business security. If you are looking for expert guidance to implement security fixes and strengthen your business defenses, contact the IT Consulting Services in Los Angeles team today.
- Re-Testing
Re-testing validates that identified vulnerabilities have been successfully addressed. This step ensures that fixes are effective and that no new issues are introduced during remediation. Regular re-testing helps maintain a secure environment and confirms that business-critical systems remain protected.
It provides confidence that actions taken are practical and support continuous improvement in security practices. Re-testing is a key step in maintaining a proactive, resilient approach to cybersecurity.
- Continuous Monitoring and Improvement
Continuous monitoring and improvement ensure security remains robust over time. Businesses track systems, networks, and applications for new vulnerabilities and evolving threats. Security measures are adjusted and strengthened based on monitoring results, industry trends, and emerging risks.
This ongoing approach helps small businesses stay ahead of cyber threats, maintain compliance, and protect sensitive data. Continuous monitoring and improvement turn penetration testing into a dynamic process that grows with the business, creating lasting security resilience.
4 Tips to Maximize Penetration Testing for Small Businesses
Small businesses can get the most out of penetration testing by following a few essential tips. These tips will help make the process efficient and effective.
- Define Clear Goals: Start by identifying what you want to achieve from the test. Focus on protecting sensitive data and critical systems to make the results actionable.
- Scope the Test Properly: Include the most critical networks, applications, and devices. Avoid unnecessary areas to save time, resources, and keep testing focused.
- Hire Qualified Experts: Work with certified penetration testers or trusted security providers who understand small business needs and can perform tests safely.
- Train Your Team: Educate employees on recognizing threats and following best practices. A well-informed team strengthens overall security.
- Document and Share Findings Clearly: Keep reports clear and easy to understand. Please share them with IT teams and decision-makers to prioritize actions effectively.
Following these tips ensures penetration testing delivers actionable insights and strengthens the business’s security posture efficiently.
Final Words
Penetration testing is an essential step for small businesses. It helps protect their data, systems, and the trust of their customers. By following a structured approach, from planning and threat modeling to remediation and continuous monitoring, businesses can uncover vulnerabilities before attackers do and strengthen their security. Regular testing, combined with proper training and expert guidance, ensures small businesses stay secure, resilient, and confident in their ability to face evolving cyber threats.