
How a Home Title Freeze Protects You from Deed Fraud and Title Theft
Owning a home is one of the proudest milestones in life. Yet, while most homeowners secure their properties with locks…
Well-Researched Information You Can Trust

Owning a home is one of the proudest milestones in life. Yet, while most homeowners secure their properties with locks…

Understanding the Importance of Security Cameras in Houston Houston is a vibrant city known for its thriving business districts, busy…

Why Investing in Security Cameras Matters Security is a top priority for homeowners and business owners alike. With the rise…

Why Professional Chimney Services Are Essential in Milwaukee A chimney is not just an architectural feature—it’s one of the most…

Colombia offers big rewards and sharp risks. Smart operators plan first. They need clear actions, local insight, and reliable support….

Introduction With the increase in the digital economy, the need to safeguard the minors against harmful or age-restricted content has…

There is nothing more hazardous for your office than an outdated security system. Often, people install security systems in their…

Suppose your organization is a thriving metropolis- rippling with immense productivity and interwoven by numerous digital roads. But as cities…

The new generation of cyber threats is more advanced, and the vintage method of using passwords to protect digital resources…
Passwords are the traditional weak point when it comes to business security. However, even after decades of investments in password…
Introduction Passwords have been the basis of digital authentication for decades. However, they have also formed one of the most…

Security is a key aspect of operating a small business. An effective system not only secures property, but also employees…

Introduction: The Moving Ground of Authentication Security in the workplace has always been a balancing game between ensuring the confidentiality…
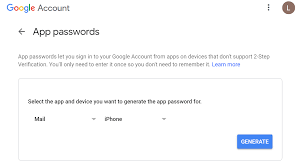
Introduction Gmail remains one of the most trusted and widely used email services in the world. As Google continues to…

Unarmed security guards provide high class safety in offices. They provide an affordable solution to various businesses. Workplaces, schools, and…
Digitization is surfacing dramatically. With remote arrangements becoming a trend, easy accessibility through mobile devices and laptops has opened doors…

Sydney’s a funny place. One minute you’re sipping a flat white in a buzzing café, the next you’re dodging a…
With the possibility of a security breach taking down a whole industry, cybersecurity could no longer reside in a separate…

However, cybersecurity has become a battlefield with more advanced forms of threats, more often and more unexpectedly. The organizations can…

Cyber threats are more threatening than ever before in the current dynamic digital world. As organizations continue to rely increasingly…
Security guards maintain order, deter crime, and ensure the safety of people and property. However, not all security guards for…

Today, industrial security goes well beyond gates, cameras, and badge readers. Engineers now build protective features right into tools, cabinets,…

In an era defined by smart technology and connectivity, the way we protect our homes has undergone a radical transformation….

Outsourcing cybersecurity is a smart move for many businesses. After all, not every company has the resources to build an…