
12 Tips on How Social Media Influencers Make the Most Money
In 2025, the producer economy will be rich. Social media influencers have evolved from creators to powerful marketing partners and…
Well-Researched Information You Can Trust

In 2025, the producer economy will be rich. Social media influencers have evolved from creators to powerful marketing partners and…

Security Operations Centers (SOCs) have now become the Central Nervous System of the modern security defense in the digital world…

Have you ever asked yourself if it’s really a good idea to accept that welcome bonus you see on slot…

Do you want a peaceful and serene travel experience away from the hustle and bustle? Then, plan your vacation away…

Imagine going on a journey that excites you and helps the planet. Dubai now offers eco-friendly tours, thanks to a…

Heuristic detection is central to threat identification in the current threat-filled cyberspace environment. Heuristic systems present an active mechanism to…
Navigating through the myriad of scholarships available to high school students can feel like steering through a labyrinth without a…

In the gearing of the world towards sustainable energy sources, Europe is well placed to lead in the photovoltaic (PV)…

Introduction Heuristic detection is an essential element of the current cybersecurity systems and allows the analysts to detect emerging threats…
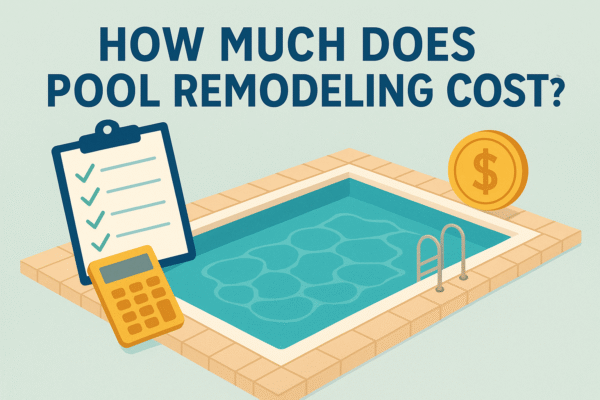
Are you a homeowner who wants to give their swimming pool a facelift, say no more because we have answers…

Cyber threats are becoming more complicated and advanced, and those methods of malware detection used earlier cannot be enough anymore….

A nice view or a pleasant site visit does not make a good home alone. Poor soil, uneven slopes, no…

In the world of digital communication, messages systems have entered our lives along with personal and professional communication. Telegram and…

With the growing complexity of the cloud environments, the old security measures are failing to keep the pace with the…

Introduction: The Cloud Computing Surge In the last ten years the world IT scenario has changed in a revolutionary way….

Introduction: The Shifting Landscape of Email-Based Threats One of the most successful and popular tools of cybercriminals is email. Easy…

Introduction: The Escalating Arms Race in Cybersecurity Email-borne attacks are among the most effective and widespread threats, which emerge in…

Introduction: The Evolution Beyond Blacklists Cybercriminals were the first to explore the weaknesses of email, as this mode of communication…

Learning of mesothelioma later in life might be abrupt and perplexing. Seniors can find special difficulties at this period. Consistent…

In today’s changing cyberwarfare battleground, perhaps no threat has followed individuals and organizations more than that of phishing. Since the…

Introduction Phishing is currently being ranked as one of the most common and devastating cyber threats in the modern internet…

Dealing with tax debt can be a harrowing experience, with its complex regulations and potentially severe consequences. Many individuals feel…

The problem of cybersecurity threats is developing at an increasingly worrying speed, and phishing and social engineering attacks may be…

Xổ số Keno là hình thức giải trí phổ biến tại V9BET nhờ cách chơi đơn giản, quay số liên…