
Strengthen Your Security Posture with Gridware’s Managed Cybersecurity
Key Highlights Introduction In today’s digital world, are you confident your business is protected from the ever-growing number of cyber…
Well-Researched Information You Can Trust

Key Highlights Introduction In today’s digital world, are you confident your business is protected from the ever-growing number of cyber…

BTCPresswire today announced further expansion of its financial media coordination framework, reinforcing its ability to support cryptocurrency, blockchain, and Web3…
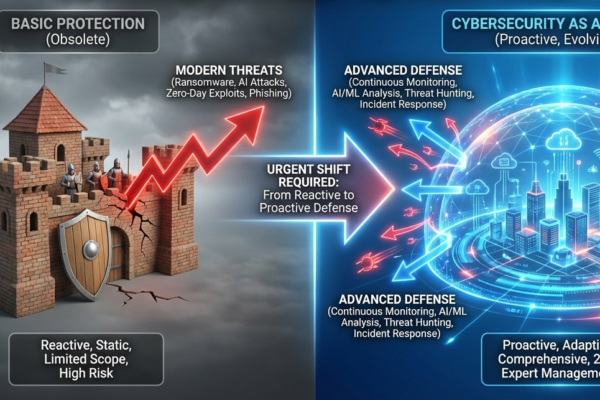
There has never been a more digitally connected business environment as seen today. The cloud environments, remote working forces, mobile…

Cybersecurity is an important issue in the digital era to ensure the protection of sensitive information, systems, and networks against…

Introduction Cybercriminals increasingly rely on deception rather than technical exploits to gain access to sensitive data. Smishing and phishing attacks…

Cybersecurity is emerging as one of the most important issues of people, companies, and governments in an interconnected world. Digital…

The Internet is now a very useful device of communication, business, education and activities in the highly connected world. Since…

Internet is now a highly needed amenity of contemporary life and is on the verge of linking billions of human…

The Internet has become so critical in the contemporary life that it facilitates communication, trade, education and entertainment within the…

We explore FTAsiaStock Crypto, an emerging digital asset platform designed to bridge traditional finance and the rapidly evolving cryptocurrency ecosystem…
Internet architecture forms the basis of the data flow between the devices around the globe. When you visit a web…

The issue of cybersecurity is one of the most important areas of contemporary digital space. With the increasing technological advancement…

With a digital system to nearly all components of our work and our everyday life, efficiency is no longer a…

Introduction: The Emerging Demand of Digital Security Today, we live in a highly connected society where individuals keep all the…

In the modern digital world, it is a risky tactic to wait to be alerted by an alarm. Active cyber…

In the hyper-connected world today, our devices, apps and operating systems are critical to our work, communication, shopping, learning and…

Privacy is one of the most precious and the most threatened commodities in the hyper connected world today. All the…

Smartphones have become an inseparable element of contemporary life. Mobile devices deal with so much personal and professional information, whether…

Nowadays, phishing with its digital era is a common and harmful hazard of internet users. They are fraudulent schemes meant…

Over the last year I’ve been deep in the vibe-coding world… yes, that strange intersection where developers, AI hobbyists, and…
I first installed NordVPN on a shaky hotel Wi-Fi connection in Istanbul — half hoping it would protect me, half…

Currently, the maritime industry is connected with the digital world, which increases the risk of cyber attacks. Therefore, it is…

With the modern digital era, social media platforms have entered society. They bind us with friends, family and societies throughout…

By 2026, cybersecurity has become more than a technology concern — it’s a foundation of economic and social stability. Every…