Two-Factor Authentication (2FA): Your First Line of Defense
In the world of today, which is more connected than ever, the protection of your online accounts is more important…
Well-Researched Information You Can Trust
In the world of today, which is more connected than ever, the protection of your online accounts is more important…

Whether it is social media, email, or a mobile bank, in the modern digital age, virtually all services we consume,…

The modern interconnected world is no longer luxurious; it has become mandatory to have access to the internet. In the…

The world of the Internet has penetrated our individual and professional lives more than ever before in the hyperlinked world…
Folkestone is a charming coastal town—but like any growing community, it’s not immune to security threats. Businesses, construction sites, events,…

Introduction: The Hybrid Cloud Success of People The adoption of the hybrid cloud is viewed in a technical perspective as…
In the ever-evolving world of social media, where opinions form and spread within seconds, understanding what’s being said about your…
Photo from Pexels Numerous organizations aim for a simple method that maintains systems’ usability while minimizing unnecessary risks, frequently depending…

Introduction In the modern world of a fast changing business environment companies are ever challenged to be agile at all…

Cloud computing is now the foundation of innovation, efficiency and scaling in the digital economy of the modern world. However,…
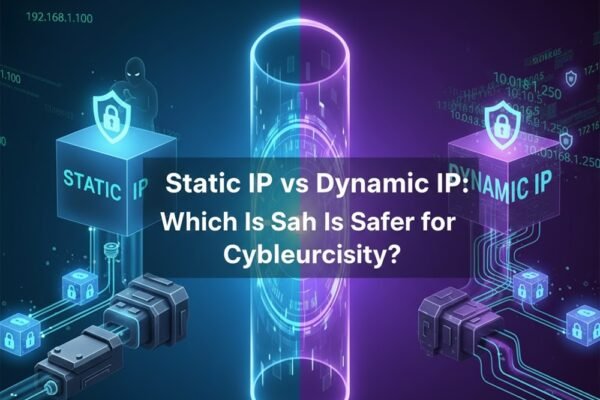
Cybersecurity is all about protecting your data from outside threats. When you connect your devices to the internet or a…

With the rise of the hyper-digital era comes increased focus on data breaches and cyber dangers. This means there is…

Cyber threats are becoming more frequent, more sophisticated, and more damaging. Thus, we come into the picture here. These days,…

In the age of increasingly advanced cyber dangers and credential theft being among the leading reasons of breaches, organizations are…

The new generation of cyber threats is more advanced, and the vintage method of using passwords to protect digital resources…

Business in Dubai is not easy. The market is huge, competition is always strong, and customers are very fast in…
Passwords are the traditional weak point when it comes to business security. However, even after decades of investments in password…
Introduction Passwords have been the basis of digital authentication for decades. However, they have also formed one of the most…

Introduction: The Moving Ground of Authentication Security in the workplace has always been a balancing game between ensuring the confidentiality…

Introduction In digital-first workplaces today, workers use dozens of business apps daily. Project management software, communication software, cloud storage, customer…

Introduction The average employee in the modern workplace is supposed to handle dozens of online accounts in one day. These…

Introduction Human error is usually the weakest link in cybersecurity. Firewalls, encryption, and intrusion detection can be the latest technology,…

In the current digital world, technology is both a hero/villain of contemporary security. Firewalls, encryption, and artificial intelligence-driven monitoring systems…

Cybersecurity has turned out to be one of the major issues of the digital age. Each click, password, or unnoticeable…