
Key Components of a Website: HTML, CSS, and JavaScript Explained
Introduction HTML, which is paired with CSS and JavaScript. These three technologies weave together to bring a site to life…
Well-Researched Information You Can Trust

Introduction HTML, which is paired with CSS and JavaScript. These three technologies weave together to bring a site to life…
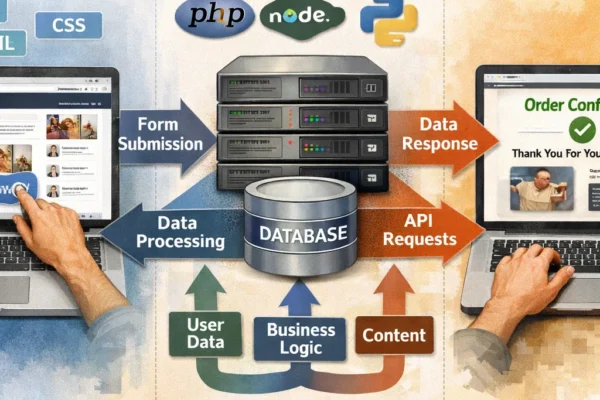
Client and server technologies. It is of great importance to developers to understand the difference between the two which play…

The development of web technologies has radically changed the way we get information, how we communicate with the digital environment,…
The web is part and parcel of our contemporary life and it has affected the way we work, interact, shop,…

Introduction In the modern digital and dynamic world, the relationship between technology and human beings has been changed significantly. We…
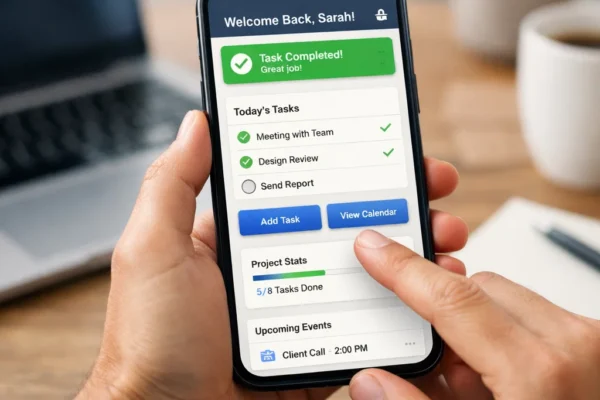
Human-Computer Interaction (HCI), in the fast changing technology world, is paramount towards defining the experience of the users and overall…

Human-Computer Interaction (HCI) is already a part of our life and it is affecting social media interactions, productivity tools in…

Introduction In the digital age, we have come to a point where tech is in almost every aspect of our…

Human Computer Interaction (HCI) is a field that is constantly in flux as it pertains to the design and use…

In our present digital age, UI’s are the elements that shape how people interact with tech. As the Internet becomes…
Introduction In the modern world of the Internet of Things, users deal with an unlimited number of interfaces, mobile applications,…

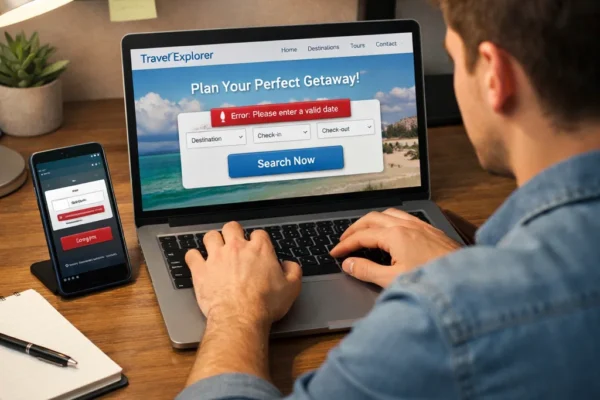
Introduction User experience (UI) is a central concept in the digital age as it can define the performance of applications,…

Introduction The user-oriented design has ceased to be a luxury in the modern digital and product-driven competitive world. Companies that…

Since the very beginning of computers, Human-Computer Interaction has experienced a metamorphosis. Since the primitive command-line interfaces up to the…
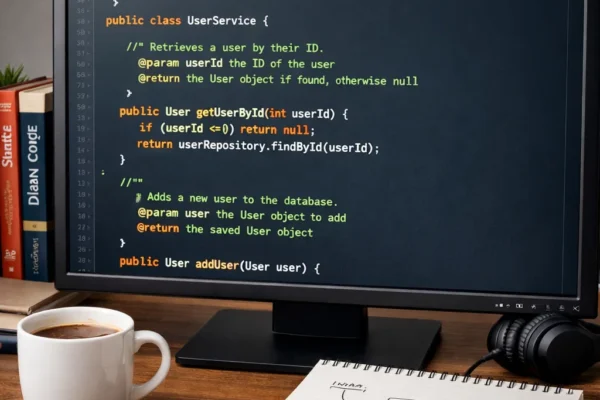
Clean and efficient Java code writing is important to developers who wish to develop maintainable, scalable, and high-performance applications. Clean…

Java web development has been essential in the development of dynamic, scalable, and secure web applications. Java has enabled web…

In the design of interactive desktop applications, a user-friendly interface should be created. Java Swing and JavaFX are the two…
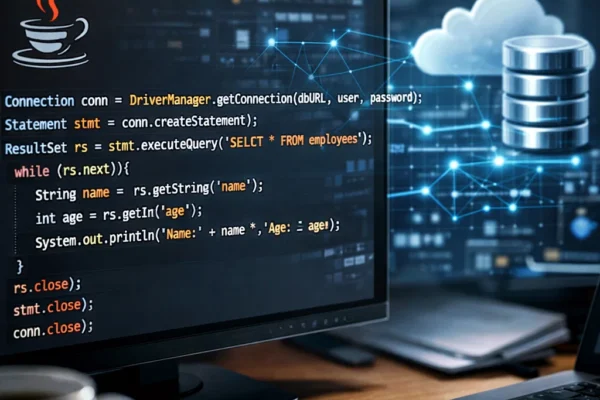
Java Database connectivity (JDBC) is a significant API exploited to allow both Java applications and databases to communicate with each…

Understanding production and costs is a key part of Economics, and it helps us see how businesses operate, make money,…

If there is one topic in Economics that follows you everywhere—from the market to your school fees—it is money. But…
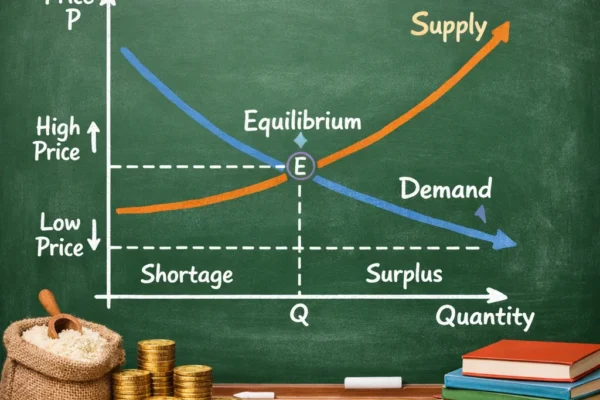
In economics, demand and supply are the pillars that explain how goods and services move in the market. Understanding these…

Economics is all around us, whether we notice it or not. From deciding how to spend your pocket money to…

Citizenship is one of the fundamental elements that define the relationship between individuals and a state. It refers to the…

Human rights are the bedrock of any just society. These fundamental rights provide the foundation for individuals to live with…