In the global digitalized world today, nearly all activities involving digitalization rely on networking. Data is always traversing systems whether you are surfing a web site, sending a text or video, streaming a video, or even having a video conference in the background. As a remedy to this complexity, a universal model referred to as the OSI model is adopted by networking experts.
The Open Systems Interconnection model is a model that is used to describe in detail the movement of data over a network in a step-by-step manner. It does not consider communication as a single complex system, but instead has segmented it into seven manageable layers.
All layers play a particular role, and a combination of all the layers guarantees a comfortable and stable connection between devices- even when the latter are entirely opposite.
In this paper we will dissect each of the layers and discuss their interactions and relate the model to practical networking, troubleshooting and cybersecurity.
What is OSI Model?
The International Organization of Standardization (ISO) came up with the OSI (Open Systems Interconnection) model in order to establish a standard language of networking systems.
Prior to the inception of OSI, networking systems did not usually work together due to the fact that the manufactures employed various approaches in communication. This was solved by the OSI model which came up with a standard layer architecture.
OSI does not have a single big communication system; instead, there are seven abstraction layers in networking, and each layer:
• Does a given job.
• Only communicates with neighboring layers.
• Depends on the layers it is on.
• Serfs the upper layers of it.
This modular design simplifies the networking design, administration and troubleshooting.
The OSI Model is still relevant today because of the following reasons. Although the importance of modern networks is based on TCP/IP model, the OSI model is of paramount importance. It helps with:
• Learning Networking Fundamentals
It provides novices with a systematic manner of learning data flow.
• Troubleshooting
Isolation of problems by layer rather than guesswork can be done by network engineers.
• System Design
OSI thinking is applied by the developers and engineers to create scalable systems.
• Cybersecurity Analysis
It is possible to analyze security threats at various levels.
• Communication Standardization
It also guarantees that various systems are still able to communicate in the same language.
Basic Idea: Encapsulation and Decapsulation.
Two important processes are important before delving into layers:
Encapsulation (Sending Data)
As the data passes down the OSI layers:
Each of these layers will add its own header (and occasionally trailer).
• In every step the data gets more organized.
• Lastly translated into signals at the Physical layer.
Decapsulation (Receiving Data)
When data arrives:
The header is stripped away by each of the layers.
• Information is re-assembled in blocks.
• Sent to the user on the Application layer.
The 7 Layers of OSI Model (Detailed Breakdown).
1. Application Layer (Layer 7) -User Interaction Layer.
This layer is the nearest to man. It is where network services are exposed to the users.
What it does:
• Offers interface between user and network.
• Supports application services such as email, browsing, file sharing.
• Enables access to network resources.
Common protocols:
• HTTP / HTTPS (browsing the web)
• SMTP (email sending)
• FTP (file transfer)
• Domain name resolution (DNS).
Real-world example:
The Application layer allows you to type in the address of a web site (e.g. Google.com) into your browser and the request is made.
Key insight:
This layer is not about such apps as WhatsApp or Chrome, but rather about the network services to which these apps are connected.
2. Presentation Layer (Layer 6) – Data Translator.
This layer makes sure that the data in the form of the receiving system is useful.
Main functions:
• Encryption and decryption of data.
• Compression and decompression
• Format conversion (ASCII, JPEG, MP4, and so on)
Real-world example:
Encryption is done when opening a secure site (HTTPS).
Why it matters:
In the absence of this layer, various systems may not be able to comprehend the data format of the other one.
3. Session Layer (Layer 5) -Communication Manager.
Session layer manages the communication between the devices.
Functions:
• Creates Inter-system sessions.
• Maintains active communication
• Ends the sessions once they are finished.
• Synchronizes data exchange
Real-world analogy:
Consider it an organizer of the meeting:
• Starts the meeting
• Keeps participants connected
• Closes the meeting in an appropriate way.
Example:
Video calls (Zoom, Google Meet) are based on the session management.
4. Transport Layer (Layer 4) -Reliable Delivery Layer.
This is a layer that guarantees full and proper delivery of data.
Core responsibilities:
• Divides data into pieces.
• Reassembles information at receiver.
• Also offers error detection and correction.
• Controls data flow
Key protocols:
• TCP (Transmission Control Protocol): ordered delivery, reliability.
• UDP (User Datagram Protocol): less reliable, but faster.
Real-world example:
In case of downloading a file, TCP does not allow any bytes to go by without being received.
5. Network Layer (Layer 3) Routing Layer.
This layer is in charge of transferring information among various networks.
Functions:
• Logical addresses (IP addresses)
• Directing information over networks.
• Deciding how to best path data.
• Packet forwarding
Devices involved:
• Routers
• Layer 3 switches
Real-world example:
In sending a message between Nigeria and a server in the US, it is this layer that determines the path.
6. Data Link Layer (Layer 2) – Data Delivery Layer (Local)
This layer guarantees the exchange of data between the devices in the same network.
Functions:
• Identifies using MAC addresses.
• Error detection (in most cases not correction)
• Creation of frame and synchronization.
• Controls access to physical medium
Sub-layers:
• LLC (Logical Link Control) is the name of the second format.
• MAC (Media access control).
Real-world example:
This layer is used in your laptop when connecting to Wi-Fi router.
7. Physical Layer (Layer 1) – Hardware Transmission Layer.
This forms the basis of OSI model.
Functions:
• Transforms data to electrical, optical or radio signals.
• Defines standards of cables, connectors and hardware.
• regulates the speed and voltage of controls.
• Handles bit-level transmission
Examples:
• Ethernet cables
• Fiber optics
• Wi-Fi signals
• Network interface cards (NICs).
Real-world example:
Only on this layer, when sending data over Wi-Fi, the data is sent in the form of radio waves.
The working of the All the OSI Layers.
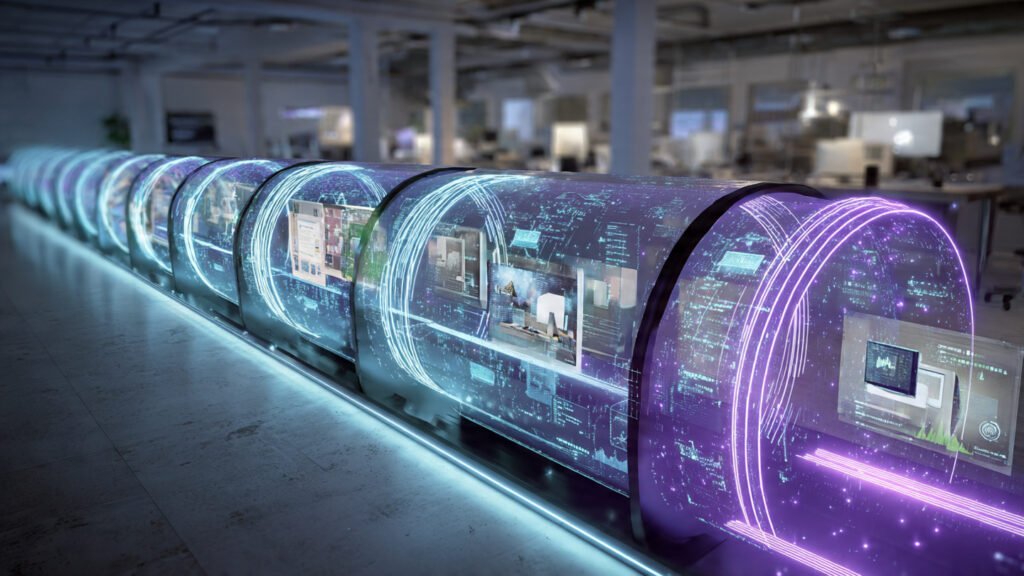
The OSI model is the model of a pipeline.
Step 1: Data sending (Top to Bottom)
• Application creates data
• Presentation formats it
• Session manages connection
• Transport segments data
• Network routes packets
• Data is linked in Data Frames.
• Physical transmits signals
Step 2: Receiving Data (Bottom → Top)
• Physical receives signals
• Frame is processed by Data Link.
• Reads IP routing information in the network.
• Transport reassembles data
• Session manages connection
• Presentation decodes format
• Application delivers to user
Real-Life Applications: Loading a Webpage.

What happens when you open a web site? This can be broken down into the following:
• Request (Application layer) is sent by browser.
• Data is encrypted (Presentation layer)
• Connection to server (Session layer) is made.
• Packets are broken down into packets (Transport layer)
• The routing of packets is through IP (Network layer).
• LAN/Wi-Fi (Data Link layer) is used to send frames.
• Signals can be carried by cables or air (Physical layer).
Then the server inverses the process and issues a response.
OSI Model vs TCP/IP Model.
OSI model is the theory and TCP/IP is the practice model.
OSI Model TCP /IP Model.
• 7 layers 4 layers
• Conceptual Real-world implementation
• ISO standard Internet standard
TCP/IP Layers:
• Application
• Transport
• Internet
• Network Access
In spite of the differences, OSI is still applied to learning and troubleshooting.
Cybersecurity and OSI Model.
The OSI layers may be vulnerable to or defended against attacks in different ways.
Examples:
• Application Layer: phishing attacks, malware.
• Presentation Layer: bypass attempts of encryption.
• Session Layer: session hijacking.
• Transport Layer: DDoS attacks.
• Network Layer: IP spoofing.
• MAC flooding: Data Link Layer.
• Physical Layer: hardware or cable tapping attacks.
Why this matters:
Threat mapping according to OSI layers assists cybersecurity professionals to defend systems better.
OSI-layer Troubleshooting.
OSI is used by network engineers to find the issues fast.
Example scenarios:
• No internet (check Physical layer (cable/Wi-Fi))
• Wrong IP → Network layer problem.
• Slowness of web site- Transport layer.
• Failure to log in- in – Application layer problem.
Benefit:
Engineers do not have to guess the problem layer, but isolate the specific problem layer.
Practical Career Relevance
The OSI model is important to understand because it is crucial in:
• Network Engineers
• Cybersecurity Analysts
• System Administrators
• Cloud Engineers
• IT Support Specialists
It is also popular in interviewing in the field of IT positions.
Common Interview Questions
• What is the OSI?
A 7 layer network communication model.
• What is the layer that does routing?
Network layer.
• Which is the difference between TCP and UDP?
TCP is more reliable; UDP is faster yet less reliable.
• Which layer deals with encryption?
Presentation layer.
Layers to Easy Mnemonic to Remember.
All the people appear to require information manipulation.
• Application
• Presentation
• Session
• Transport
• Network
• Data Link
• Physical
Key Takeaways
OSI model standardizes the network communication.
It is made up of 7 layers that have particular functions.
• There is a top-down (sending) data flow and bottom-up (receiving) data flow.
• It is vital to networking, security and troubleshooting.
• Continues to be popular in education and IT sectors.
Conclusion
The OSI model has been among the most significant networking basics. Although in contemporary systems TCP/IP is used, the OSI model gives a good mental picture of how the flow of data among systems occurs.
It simplifies a complex process through the division of communication into seven ordered layers which make it logical and manageable.
By having full knowledge of the OSI model you are able to:
• Quickly diagnose network problems.
• Learn about the working of the internet.
• Learn more about IT and cybersecurity.
To put it in brief the OSI model is not mere theory it is the blue print on which all your digital communications are today.



